In today’s interconnected world, the internet serves as a double-edged sword, offering vast resources at our fingertips while exposing us to cybersecurity threats. Leisurely browsing in a café or scrolling through emails in a park can unknowingly make us targets for hackers. Public Wi-Fi networks, often lacking robust security measures, become hunting grounds for these cyber predators, exploiting vulnerabilities to access personal information.
The Hidden Dangers of Public Wi-Fi
When you connect to public Wi-Fi, you’re stepping into a digital battlefield, often unaware of the eyes prying on your online activities. Hackers, skilled in the art of digital eavesdropping, exploit these networks to perform man-in-the-middle attacks. Imagine sitting in a café, casually checking your bank account or logging into your social media profiles, not realizing that someone might be intercepting those precious bits of data. This scenario isn’t just hypothetical; it’s a common reality in today’s digital age. Public Wi-Fi, for all its convenience, is a minefield of cybersecurity threats. It’s akin to having a conversation you think is private, only to discover someone has been listening in the whole time. The necessity for a secure digital life becomes glaringly apparent as we navigate through these invisible dangers. Adopting proactive security measures transforms from a recommendation to an imperative, ensuring our digital endeavors don’t turn into vulnerabilities.
Nice to know
To assess the security of a public network as a private user, it’s crucial to be aware of specific indicators that might signal potential security risks. One of the initial steps involves checking the network authentication. A secure network typically requires some form of authentication, whether it’s a password or another security check, before allowing a connection. Networks without any form of authentication are more susceptible to man-in-the-middle attacks and other types of data exploitation.
Another vital tip is to verify the network name (SSID). Hackers often set up fake networks with similar or familiar-sounding names to trick users into connecting with them. Therefore, always double-check the exact name of the network to ensure you are connecting to the official network of the café, hotel, or any other public place.
For an added layer of security, users can also review the network’s encryption. Modern and secure networks utilize WPA2 or WPA3 encryption to protect transmitted data. If a network uses outdated WEP encryption or shows no signs of encryption, it’s a red flag that the network may not be secure.
Diving Deep into the Abyss of Data Breaches
The annals of cyber history are stained with incidents of massive data breaches, each narrating a tale of security oversight leading to disastrous consequences. Consider the breach that struck a major retailer, where hackers accessed the financial information about millions of customers, or the social media giant that inadvertently exposed the personal details of its users. These aren’t just cautionary tales; they’re stark reminders of the fragility of digital security. The common denominator in these incidents is the exploitation of vulnerabilities within seemingly secure systems. The aftermath of these breaches extends beyond the immediate financial repercussions; it erodes the foundational trust between users and platforms.
Erecting Digital Fortresses with VPN Services
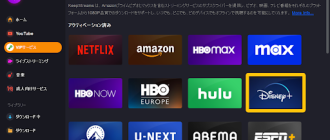
In the quest for impenetrable online security, Virtual Private Networks (VPNs) stand as guardians of privacy. These digital fortresses offer more than just encryption; they provide anonymity, creating a cloaked pathway for your online activities. Imagine sending your data through a secure tunnel, invisible and inaccessible to prying eyes. This isn’t just about protecting yourself on public Wi-Fi; it’s about creating a shield around your digital life, wherever you are. VPNs serve as the armor in your cybersecurity arsenal, defending against the ever-present threat of data interception. Whether you’re browsing from the comfort of your home or the local coffee shop, a VPN ensures that your online presence remains private and protected.
Enhancing Mobile Security with VPN Implementation
Securing mobile devices with a VPN is not just a recommendation; it’s a necessity in the digital age. The process is surprisingly user-friendly, designed to accommodate even those with minimal technical expertise. Reputable VPN providers have made significant strides in simplifying the installation process. They offer intuitive applications that lead users step-by-step through downloading, installing, and activating the VPN service. The key to a successful setup lies in selecting a trustworthy VPN provider. Look for services with strong encryption protocols, a no-logs policy, and positive user reviews. Once the application is installed from a reliable source, users can easily activate the VPN, often with just a tap. Configuring the VPN to start automatically ensures continuous protection, safeguarding data transmission even during those moments of forgetfulness.
Navigating the Treacherous Waters of Phishing Scams
Phishing scams, sophisticated in their deceit, pose a significant risk to online safety. These digital deceptions cleverly disguise themselves as legitimate communications, from emails mimicking financial institutions to messages that seem to be from known contacts. The sophistication of these scams requires a keen eye and a critical mindset. Vigilance begins with scrutinizing the sender’s email address and looking out for unusual language or urgent requests that seem out of character. Implementing two-factor authentication provides an additional security layer, making it harder for attackers to gain unauthorized access even if they manage to deceive you into providing sensitive information. Education plays a crucial role in defense; familiarizing oneself with the latest phishing techniques and sharing this knowledge can create a community of informed users less susceptible to these attacks.
The Ongoing Odyssey of Cyber Vigilance
In the realm of cybersecurity, complacency is the enemy. The digital landscape is ever-changing, with new threats emerging as quickly as technology advances. Keeping software up to date is not just about accessing the latest features; it’s about closing security gaps that could be exploited by cybercriminals. Password management is another cornerstone of personal cybersecurity. Utilizing complex, unique passwords for different accounts and employing a reputable password manager can significantly reduce the risk of unauthorized access. Moreover, cybersecurity awareness is not a one-time lesson but a continuous journey of learning. Engaging with cybersecurity news, participating in online safety workshops, and staying informed about evolving cyber threats are essential practices.